The code warriors of the future literally might be computer code acting as warriors to defend against attackers on computer networks.
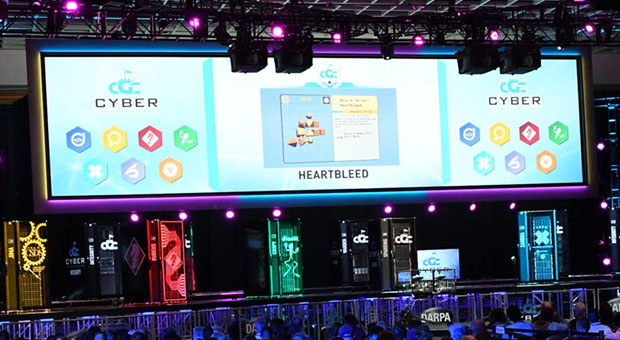
The Defense Advanced Research Projects Agency, or DARPA, gave us a glimpse into that future last Sunday, when it announced the winners of its Cyber Grand Challenge at DEF CON.
Seven teams participated in the challenge to create systems that used bots to find and fix software problems without human intervention.
“Our mission is to change what’s possible, so that we can take huge strides forward in our national security capabilities. And if that’s what our job is every single day, I think we did it today,” said DARPA Director Arati Prabhakar.
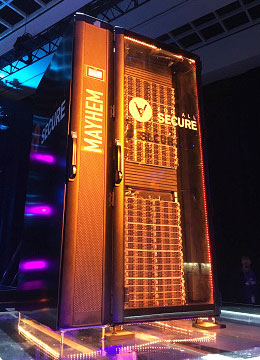
Taking home the US$2 million grand prize was ForAllSecure, a startup founded by a team of computer security researchers from Pittsburgh, for its Mayhem system.
Winning the second place prize of $1 million was TECHx, made up of a team of software analysis experts from GrammaTech and the University of Virginia in Charlottesville.
Third place finisher, Shellphish, a group of computer science graduate students at the University of California-Santa Barbara’s SecLab, won $750,000.
Breaking Lock-Picks
The teams participating in the event spent three years getting their systems in shape for the world’s first all-machine hacking tournament.
Once the competition commenced, the bot teams played a version of “capture the flag,” a game often played by human hackers to diagnose and patch flaws in a real time adversarial environment.
Sparks flew for eight hours and 96 rounds of action, until the machines had created 421 replacement binaries that were more secure than the original code, and authored 650 unique proofs of vulnerability in the software they scrutinized.
“There’s a saying in the hacker community that ‘zero day can happen to anybody.’ What that means is that unknown flaws in software are a universal lock-pick for intruders,” DARPA CGC Program Manager Mike Walker said.
“Tonight we showed that machines can exist that can detect those lock-picks and respond immediately,” he continued. “We have redefined what is possible, and we did it in the course of hours with autonomous systems that we challenged the world to build.”
Out of Comfort Zone
Some vendors already are carrying out machine scanning and fixing of known vulnerabilities, noted Amol Sarwate, director of vulnerability labs at Qualys.
“What DARPA is targeting is unknown vulnerabilities, or zero-day vulnerabilities,” he told TechNewsWorld.
While the systems used in the challenge need additional refinement, they are valuable for DARPA’s goals.
“What DARPA does with these challenges is spark interest and show the world what’s possible,” said Sarwate.
With the Grand Challenge, DARPA is trying to get the security industry out of its comfort zone, suggested Rami Essaid, CEO of Distil Networks.
“We in the security industry have always been reactive to issues. What DARPA is trying to do is, through automation, is get us to be proactive about flaws and security vulnerabilities,” he told TechNewsWorld.
“They’re showing us we don’t have to wait and react to issues — that by using some sort of automation, some sort of machine intelligence, we can get out ahead of issues that pop up,” Essaid pointed out. “It’s a more forward way of doing cybersecurity.”
Human-Machine Mix
Software security today is shared between humans and machines.
“It’s currently left up to humans through manual creative review to identify everything that software has missed, and the gap is too big,” said Alex Rice, CTO of HackerOne.
“The DARPA Grand Challenge is about significantly increasing the ability of machines and technology systems to identify vulnerabilities that have been missed by their authors,” he told TechNewsWorld.
The idea is not to replace humans in the process, but to get machines to pick up more of the load.
“For the foreseeable future, we are going to absolutely need the power of human creativity applied to this problem,” Rice said.
“What is clear is the gap between what humans do and machines do needs to be narrowed. There aren’t enough capable people to identify all the vulnerabilities out there without significantly more help from computer systems,” he explained. “None of the winners of the challenge had a perfect score. If we’re not close to getting a perfect score in a simulated environment, we’re not going to approach it in a real environment.”
IOT Threat
Changes in the software development environment are making the need for DARPA bot warriors even more urgent.
“Software has radically changed in the last decade,” said Chandra Rangan, vice president of marketing for Hewlett Packard Enterprise. “We used to build software on a yearly time frame. Now new versions are pushed out on almost a weekly basis.”
With that shortening of the development cycle there has been an increase in software flaws.
“One out of five applications have one or more critical security flaws. Mobile applications are worse — one out of three,” he told TechNewsWorld. “We’re seeing more vulnerabilities because traditional rigor sometimes is missing.”
The problem will get worse when Internet of Things devices flood the market.
“The problem is going to be astronomical with the growth of IoT and connected devices,” said Ram Mohan, chief technology officer at Afilias.
“A lot of IoT devices don’t consider security in their design,” he told TechNewsWorld, “so you’re going to have a gaping hole where these devices don’t have the capability to upgrade. They’re going to be released in the wild and be there for life.”