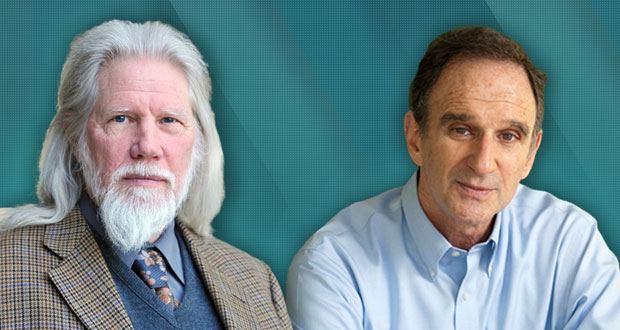
TheAssociation of Computing Machinery on Tuesday named Whitfield Diffie and Martin E. Hellman recipients of the 2015 ACM A.M. Turing Award for their contributions to modern cryptography.
Their invention of public key cryptography and digital signatures revolutionized computer security, the organization said.
The award, considered the Nobel Prize of computing, includes a US$1 million prize, with financial support provided by Google.
It is named for Alan M. Turing, the British mathematician who articulated the mathematical foundation and limits of computing. He was a key contributor to the Allied cryptoanalysis of the German Enigma cipher during World War II.
Overdue Recognition
Cryptography is a system that converts or encrypts readable information into gibberish. Only those with a designated decryption key can read the content.
“It is long overdue for this recognition of Whit Diffie and Martin Hellman’s contributions to not only cryptography, but to the mechanisms that underpin essentially all electronic commerce,” said Bobby Kuzma, a systems engineer atCore Security.
“It is well deserved,” he told TechNewsWorld.
Cryptographic Directions
Diffie and Hellman published in 1976 a paper titled “New Directions in Cryptography” that showed that asymmetric or public key cryptography was possible. That paper described the future use of computer networks in a world where sensitive information would be stolen or altered.
Forty years later, their forecasts have come true, ACM President Alexander L. Wolf said.
“Their contributions are immeasurable. The contributions have provided the fundamental mathematical principles that are still being leveraged in modern cryptography today,” Jerald Dawkins, CTO ofTokenEx.
“While protocols and their use within technology changes, these principles have proven viable over time,” he told TechNewsWorld.
Individuals communicate privately over a secure channel with banks, e-commerce sites, email servers and the cloud on a daily basis, the ACM said.
Public key cryptography and digital signatures are the foundation for most regularly used security protocols on the Internet today, according to the organization. The Diffie-Hellman Protocol protects daily Internet communications and trillions of dollars in financial transactions.
Master Engineers
Diffie was chief security officer of Sun Microsystems and now serves as a consulting scholar for the Center for International Security and Cooperation at Stanford University.
He worked throughout the 1990s to protect individual and business rights to use encryption. He is a Marconi fellow and the recipient of a number of awards, including the National Computer Systems Security Award given jointly by NIST and the NSA and the Franklin Institute’s Levy Prize.
Hellman is professor emeritus of electrical engineering at Stanford. He is a member of the National Academy of Engineering and an inductee of the National Inventors Hall of Fame. He is best known for his inventing public key cryptography with Diffie and Ralph Merkle.
He also was a long-time contributor to the computer privacy debate. He was involved with the issue of DES key size in 1975 and served from 1994 to 1996 on the National Research Council’s Committee to Study National Cryptographic Policy, whose main recommendations have since been implemented.
“Cryptography is the foundation on how we ensure confidentiality and integrity of information at rest and during transmission. It allows us to gain trust in digital information that otherwise could not be accomplished,” TokenEx’s Dawkins said.
Essential Service
“Cryptography is essential for ensuring our security and privacy,” said Core Security’s Kuzma. “Recent attacks against the Diffie-Hellman key exchange show the implications of allowing back doors and flawed implementations leading to compromises.”
Two of the greatest challenges to cryptography and the safety it affords are secrecy and governmental meddling. Trusted cryptographic systems must be open for review and analysis, and the implementations must be similarly open, he noted.
“Otherwise, we run the risk of simple flaws greatly impacting our security, privacy and safety,” Kuzma warned.
Cryptography continues to face challenges today. The fundamental properties have not changed, but their implementations and use within various protocols have, according to Dawkins.
“The most significant challenge that we face today is really not the mathematical challenges as much as its implementation by man,” he said. “Flaws in implementations include key generation, management, storage and distribution.”