The next generation of Intel mobile processors will include malware protection built into the chip, the company announced Monday.
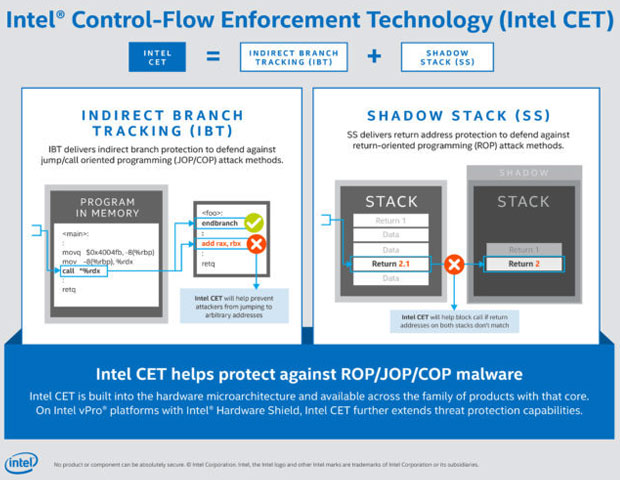
The protection, provided by Intel’s Control-Flow Enforcement Technology (CET), will first be available in the company’s “Tiger Lake” mobile processors, Vice President of Intel’s Client Computing Group Tom Garrison revealed.
CET is designed to protect against the misuse of legitimate code through control-flow hijacking attacks, which is widely used in large classes of malware, he explained.
Of the 1.097 vulnerabilities Trend Micro discovered through its Zero Day Initiative from 2019 to today, 63.2 percent were related to memory safety.
“As more proactive protections are built into the Windows OS, attackers are shifting their efforts to exploit memory safety vulnerabilities by hijacking the integrity of the control flow,” noted David Weston, director of Enterprise and OS Security at Microsoft.
“As an opt-in feature in Windows 10, Microsoft has worked with Intel to offer hardware-enforced stack protection that builds on the extensive exploit protection built into Windows 10,” he explained, ” to enforce code integrity as well as terminate any malicious code.”
Chip-Level Attacks
With control-flow protections built into Intel’s hardware, it will be possible to detect memory attacks earlier in the process, noted Ray Vinson, senior product manager atSpirent, a telecommunications testing company in Sunnyvale, California.
“The attacker is making chip-level calls to initiate the memory attack. Software sees those calls, but only after they’re made,” he told TechNewsWorld.
“By addressing the attack at the chip level, you’re preventing the calls from ever taking place and preventing any resources from being taken up by the attack,” Vinson explained.
“Memory overflow and software overflow attacks have been around as threats for years. By addressing this at the chip level, it starts to take this out as an option for the hacker,” he added.
Among the leading malware attacks currently mounted by hackers are “fileless” attacks, where malicious code is loaded directly into memory, noted James McQuiggan, security awareness advocate for KnowBe4, a security awareness training provider in Clearwater, Florida.
“This style is difficult for antimalware applications to detect, since they look for binary, executable applications running from a hard drive,” he told TechNewsWorld.
“Having the hardware join the fight against malicious software can decrease the successful attacks against endpoints in an organization’s infrastructure,” McQuiggan said. “It adds another layer of protection between the human and the operating system’s protective software to secure the endpoint and prevent a malware attack.”
Building security into the hardware architecture makes it much harder for an attacker to write successful exploits, said Nilesh Dherange, CTO of Gurucul, a risk intelligence company at El Segundo, California.
“This is a good move, potentially mitigating entire families of malware threats,” he told TechNewsWorld.
No Silver Bullet
There can be advantages and disadvantages to baking security into hardware, noted Malek Ben Salem, Americas Security R&D lead for Accenture, a professional services company based in Dublin.
“Software is more flexible. You can deploy it on more architectures, and you can deploy it faster,” she told TechNewsWorld.
“In hardware, though, you get less performance degradation, and it’s more effective in these kinds of attacks,” Ben Salem continued.
Organizations should take care not to embrace the technology too rapidly, cautioned KnowBe4’s McQuiggan.
“What impact will the hardware have from falsely stopping instructions because it was considered an attack?” he asked. “While this is a new technology, organizations will want to make sure it’s adequately configured for their environments and not just expect it to stop all malware.”
CET is no silver bullet against all attacks, warned Chris Clements, vice president of solutions architecture at Cerberus Sentinel, acybersecurity consulting and penetration testing company in Scottsdale, Arizona.
“Attackers routinely find ways to circumvent security protections, and depending on Intel’s implementation, the safeguards may turn out to be trivial to bypass,” he told TechNewsWorld.
“Further, many breaches and ransomware attacks come not from cybercriminals exploiting vulnerable software, but rather from configuration errors like open S3 buckets, weak user passwords, and social engineering attacks like phishing,” Clements continued. “In these cases, no advanced exploit development is necessary to compromise their victim’s systems or data.”
Living in a Software-Defined World
Added security in silicon is always a welcome addition, especially when dealing with memory re-use and buffer overflows, but it needs to be put in perspective.
“There is a long history of chipmakers over-reaching on embedding security in the chip and promising security gains that haven’t been there. McAfee’s acquisition by Intel was such a case,” observed Greg Young, vice president of cybersecurity atTrend Micro, a cybersecurity solutions provider headquartered in Tokyo.
“So, hardware-assisted control flow is good, especially for embedded devices, but not a game-changer, as infrastructure and endpoints have never been self-defending and the bulk of attacks don’t involve this vector,” he told TechNewsWorld.
“It’s a software-defined world, and with so much software in the stack, there’s a lot of vulnerabilities to go after that don’t involve the chip,” Young said.
There’s another potential snag for CET, Dherange pointed out.
“The implementation, as described, is an opt-in solution, which means that some developers won’t expend the effort needed to integrate with CET,” he said. “That would leave their applications potentially vulnerable.”
Nevertheless, “given the prevalence of ‘memory safety’ vulnerabilities that CET addresses, this could be of huge benefit. The challenge will be how tightly developers adhere to it,” Dherange maintained.
CET isn’t the only way to combat memory-based attacks, said Joe Saunders, CEO of RunSafe Security, an embedded systems security company in McLean, Virginia.
“Once developers start deploying on such hardware, they will need to consider the tradeoffs in performance overhead when considering enabling these protections at the hardware level,” he told TechNewsWorld.
“There are alternative approaches, such as function-level load time randomization, that eliminate memory-based attacks without overhead performance impact or trade off,” Saunders said.
CET won’t eliminate software protections and malware and antivirus tools, Accenture’s Ben Salem explained.
“This is another layer of defense that’s monitoring what’s happening in real time,” she said, “compared to software tools that are looking at malware files upline or in a sandbox environment.”