
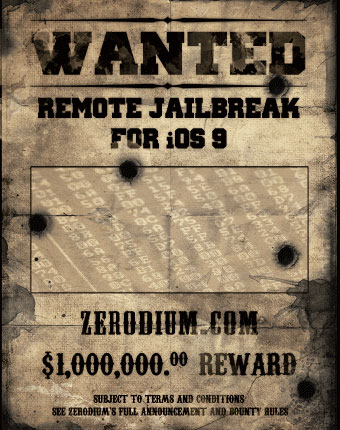
Zerodium last week posted a million-dollar bounty for juicy iOS 9 bugs or jailbreaks.
Zerodium runs a market where exploits and vulnerabilities are bought and sold, according toDamballa.
“While there is no insight into a specific buyer, we can assume if an exploit for iOS 9 is found, Zerodium will sell it for way more than (US)$1 million,” wrote Loucif Kharouni, senior threat researcher at Damballa, in a company blog post.
“Finding an iOS 9 security breach would have severe repercussions for millions of iPhone users, which have traditionally been given a higher grade for security than Android because of their ‘walled garden’ approach to Apps,” he noted.
Will Bounty Be Paid?
While cybercriminals are known to pay well for flaws that can be used to line their pockets with loot, “that’s a lot of money for an exploit,” Kharouni told TechNewsWorld. “The bounty is a way to encourage people to find those exploits. What better way to encourage people to do something than to give them a lot of money to do it?”
Will someone really get a million bucks for an iOS 9 exploit?
“When someone gets in touch with them, we’ll see if the bounty is real or not,” Kharouni said.
However, any bounty award will be difficult to confirm, he pointed out. “Anyone who tried to collect the bounty will want to remain anonymous, whether he gets paid or not.”
It’s a difficult path for any bounty hunter wishing to bag the cool million, Kharouni continued. “It’s a challenge to find an exploit for iOS, because it’s way more secure than Android.”
RAT Hunting
Zerodium has set high standards for the kinds of exploits that would qualify for the iOS 9 bounty.
“For a million bucks, they want something more than something that just steals pictures,” Kharouni noted. “They want something that will give them full access to a phone, like a RAT.”
A RAT, or remote access Trojan, gives an intruder remote control over a device.
A number of high-tech companies offer bounties to help plug holes in their software programs. They may pay $10,000 to $15,000 for a significant exploit. Those amounts face tough competition from the underground market, however.
“I’ve seen some hackers claiming to have a $400,000 budget for bug bounties and willing to pay two to three times what’s offered by a company bounty program,” said Kharouni.
More Apple Problems
As Zerodium began trawling for iOS 9 bugs, Apple was busy snuffing out security fires.
First, it discovered that hundreds of apps infected with malware had been uploaded to its App Store.
Then, as it scrambled to clean up bugs in the initial release of iOS 9, a lockscreen vulnerability was found in the OS.
The malicious app problem emerged after researchers found that Chinese developers were downloading a counterfeit version of Xcode, a tool Apple distributes to developers working on iOS apps.
Unknown to the developers, the bogus version of the tool infected the apps they were creating with malware called “XcodeGhost.”
Convenience Trumps Security
The reason the developers were downloading the flawed tool was that it was hosted on servers where it could be downloaded much faster than it could from Apple’s servers located in the United States.
As Apple went about purging the pernicious apps from its ecosystem, it committed itself to making sure the incident was not repeated in the future.
Apple will be setting up servers in China so the company’s development tools can be downloaded faster there, SVP of Worldwide Marketing Phil Schiller reportedly said last week.
Although the snafu tarnished Apple’s sterling security reputation, it could have been much worse, suggested Appthority.
“Given our risk analysis results of infected apps regarding their actual behavior, we feel that it would have been easy to add more harmful behaviors to the code and we might see that in the future, but the author of XCodeGhost chose not to implement them in the versions we analyzed,” wrote Andreas Weinlein, an engineer at Appthority.
Quicksand for Bad Apps
“The recent exploit on Apple has shown us that even Apple’s system can be compromised quite easily,” observed Filip Chytry, a security researcher with Avast.
“While this time nothing significant happened, it is a reminder that having everything under an Apple system could potentially make a system vulnerable,” he told TechNewsWorld.
“If hackers are able to exploit one entry point, they are able to attack all of the other iOS devices — and the fact that Apple doesn’t have a big variety of products makes it easier,” Chytry pointed out.
However, Apple’s use of “sandboxing” within iOS offers its users a measure of security from attacks by malicious apps.
“As part of the sandboxing process,” Chytry said, “the system installs each app in its own sandbox directory, which acts as the home for the app and its data. So malware authors cannot easily access sensitive data within other apps.”
Lockscreen Snag
Past versions of iOS have been afflicted with lockscreen vulnerabilities, and that was the case with iOS 9, too.
Jose Rodriguez, who discovered a lockscreen bug in iOS 6.1.3 two years ago, exposed the iOS 9 lockscreen flaw. He demonstrated a way to bypass the lockscreen by exploiting iOS 9’s five-attempt lockout policy when Siri is activated from the lockscreen. Once the lockscreen is bypassed, an intruder can access a phone’s photos and contacts.
“Every major upgrade represents the potential to reveal and increase an attack surface on a given device, because software is made by humans and there are market pressures to get the device to market — even if there are some small number of bugs that have yet to be found,” explained Cameron Camp, a senior researcher with Eset.
“No locking technology implementation is perfect,” he told TechNewsWorld, “and with every novel approach, there are likely to be bugs along the way. Hopefully, responsible disclosure and code reviews will serve to minimize the exposure time and rapidly deploy patches to help consumers.”
Breach Diary
- Sept. 21. Sophos reports resurgence of Facebook “dislike” button scams. Web surfers attempting to install the button are redirected to bait-and-switch websites which attempt to cajole personal information from them.
- Sept. 21. Popular photo-sharing website Imgur reports it has removed malicious javascript from site that infected its visitors’ computers and used them to participate in DDoS attacks on hacker watering holes 4chan and 8chan.
- Sept. 21. U.S. Department of Commerce’s National Institute of Standards and Technology (NIST) announces award of nearly US$3.7 million for three pilot projects designed to make online transactions more secure and private for healthcare, government services, transportation and the Internet of Things.
- Sept. 22. Trend Micro releases report including finding that credit and debit card breach incidents have increased 169 percent in the past five years.
- Sept. 22. R.T. Jones Capital Equities Management agrees to pay $75,000 and to be censured to settle charges brought by the U.S. Securities and Exchange Commission. The investment firm allegedly failed to have a cybersecurity policy in place when a data breach at a third-party provider compromised personal information of 100,000 people, including some of its clients.
- Sept. 22. Apple Senior Vice President for Worldwide Marketing Phil Schiller tells Chinese publication Sina that his company is taking steps to avoid repeat of incident where counterfeit versions of an Apple developers’ tool was used to infect programs uploaded to the Apple App Store.
- Sept. 23. U.S. Office of Personnel Management reports 5.6 million fingerprint records were stolen in massive breach of government computer systems in June, 4.5 million more than initially reported.
- Sept. 23. Provincial government of British Columbia, Canada reveals an unencrypted hard drive containing personal information on 3.4 million students has gone missing. The government says drive was supposed to be located in a locked warehouse but when they looked for it, it wasn’t there.
- Sept. 23. Galen Marsh pleads guilty in a New York City federal court for the unauthorized taking of 730,000 records away from Morgan Stanley. The investment bank says no customers lost any money as a result of the incident.
- Sept. 23. U.S. District Court in Pennsylvania rules Fifth Amendment, which bars the government from compelling a citizen to make self-incriminating admissions, protects passcodes on locked smartphones.
- Sept. 24. PR Newswire resets passwords for all journalists on its system. Service was one of several newswires breached by overseas hackers seeking information for insider trading on U.S. stock exchanges.
- Sept. 25. President Barack Obama and President of China Xi Jinping announce “common understanding” to combat theft of intellectual property over computer networks.
- Sept. 25. Security blogger Brian Krebs reports banks have discovered a pattern of credit card fraud at gift shop and restaurant point-of-sale registers at a large number of Hilton Hotels and franchise properties across the United States. Hilton confirmed to Krebs that it is investigating the claims.
- Sept. 25. North Oldham High School in Kentucky begins notifying 2,800 current and former students that their personal information, including Social Security numbers, was compromised through a Web browser attack on a nutritional service employee’s computer.
- Sept. 25. The Intercept reports British spy agency GCHQ is running program called “Karma Police” with goal to record the website browsing habits of “every visible user on the Internet.” Report is based on documents leaked by Edward Snowden.
Upcoming Security Events
- Oct. 2-3. B-Sides Ottawa. RA Centre, 2451 Riverside Dr., Ottawa, Canada. Free with registration.Oct. 6. SecureWorld Cincinnati. Sharonville Convention Center, 11355 Chester Rd., Sharonville, Ohio. Registration: open sessions pass, $25; conference pass, $175; SecureWorld plus training, $545.
- Oct. 6. UK Cyber View Summit 2015. 6 a.m. ET. Warwick Business School, 17th Floor, The Shard, 32 London Bridge, London, UK. Registration: 550 euros plus VAT.
- Oct. 9-11. B-Sides Warsaw. Pastwomiasto, Anders 29, Warsaw, Poland. Free with registration.
- Oct. 12-14. FireEye Cyber Defense Summit. Washington Hilton, 1919 Connecticut Ave. NW, Washington, D.C. Registration: before Sept. 19, $1,125; after Sept. 18, $1,500.
- Oct. 13. Protecting Your Users from Online Attackers. 2 p.m. ET. Dark Reading webinar. Free with registration.
- Oct. 14. Latest DDoS Attacks Trends — Excerpts from Arbor ATLAS Global Statistics. 10 a.m. ET. Webinar by Arbor Networks. Free with registration.
- Oct. 14. Best Practices in DDoS Defense: Real World Customer Perspectives. 11 a.m. ET. Webinar sponsored by Networks. Free with registration.
- Oct. 14. Arbor Solutions for the Next Decade of DDoS Defense. 9 a.m. ET. Webinar sponsored by Arbor Networks. Free with registration.
- Oct. 15. SecureWorld Denver. The Cable Center, 2000 Buchtel Blvd., Denver, Colorado. Registration: open sessions pass, $25; conference pass, $175; SecureWorld plus training, $545.
- Oct. 15-16. B-Sides Los Angeles. Dockweiler Youth Center and State Beach. Free.
- Oct. 16-18. B-Sides Washington D.C. Washington Marriott Metro Center, 775 12th St NW, Washington, D.C. Free.
- Oct. 17-18. B-Sides So Paulo. Pontifcia Universidade Catlica de So Paulo, So Paulo, Brazil. Free.
- Oct. 19-21. CSX Cybersecurity Nexus Conference. Marriott Wardman Park, 2660 Woodley Rd. NW, Washington, D.C. Registration: before Oct. 14 — member, $1,595; nonmember, $1,795. After Oct. 14 — member, $1,795; nonmember, $1,995.
- Oct. 28. The Cyber-Centric Enterprise. 8:15 a.m. ET. Virtual conference. Free with registration.
- Oct. 28-29. SecureWorld Dallas. Plano Centre, 2000 East Spring Creek Parkway, Plano, Texas. Registration: open sessions pass, $25; conference pass, $175; SecureWorld plus training, $545.Oct. 28-29. Securing New Ground. Conference sponsored by Security Industry Association. Millennium Broadway Hotel, New York City. Registration: after Sept. 7 — member, $1,095; nonmember, $1,495; CISO, CSO, CIO, $300.
- Nov. 4. Bay Area SecureWorld. San Jose Marriott, 301 South Market St., San Jose, California. Registration: open sessions pass, $25; conference pass, $175; SecureWorld plus training, $545.
- Nov. 10. FedCyber 2015 Annual Summit. Tyson’s Corner Marriott, 8028 Leesburg Pike, Tyson’s Corner, Virginia. Registration: $395; academic, $145; government and military, free.
- Nov. 11-12. Seattle SecureWorld. Meydenbauer Center, 11100 NE 6th St., Bellevue, Washington. Registration: open sessions pass, $25; conference pass, $175; SecureWorld plus training, $545.
- Nov. 13-14. B-Sides Delaware. Wilmington University, New Castle Campus, 320 North Dupont Highway, New Castle, Delaware. Free with registration.
- Nov. 24-25. Cyber Impact Gateway Conference. ILEC Conference Centre and Ibis London Earls Court, London, UK. Registration: Before Oct. 9 — end users, Pounds 1,799 plus VAT; solution providers, Pounds 2,799 plus VAT. Before Oct. 30 — end users, Pounds 1,899 plus VAT; solution providers, Pounds 2,899 plus VAT. Standard — end users, Pounds 1,999 plus VAT; solution providers, Pounds 2,999 plus VAT.
- Dec. 12. Threats and Defenses on the Internet. Noon ET. Northeastern University, Burlington Campus, 145 South Bedford St., Burlington, Massachusetts. Registration: $6.




















































