A phishing scam that surfaced earlier this week used Google Docs in an attack against at least 1 million Gmail users.
However, that amounted to fewer than 0.1 percent of Gmail users were affected, according to the company.
Google last year put the number of active monthly Gmail users at more than 1 billion.
Google shut down the phishing scam within an hour, it said, through both automatic and manual actions. It removed the fake pages and applications, and it pushed updates through Safe Browsing, Gmail and other anti-abuse systems.
Users did not need to take any action on their own in response to the attack, Google said, but those who wanted to review third-party apps connected to their account could do so at its Security Checkup site.
Anti-Phishing Security Checks
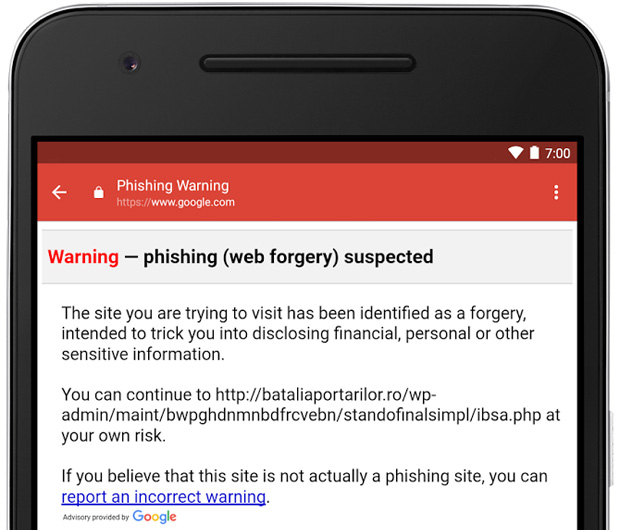
Coincidentally, Google this week introduced a new anti-phishing security feature to Gmail on Android. The new tool delivers a warning when a user clicks on a suspicious link in an email message, alerting them that the site they’re trying to visit has been identified as a forgery. Users can back away or continue to the site at their own risk.
Google is gradually rolling out the new feature to all G Suite users.
How the Docs Attack Went Down
This week’s Docs attack was an effective approach to luring users before Google clamped down.
People got an email from someone they knew inviting them to click on a link to collaborate on a Google Doc.
Clicking on the “Open in Docs” link redirected them to a Google OAuth 2.0 page to authorize the Google Docs application, which was a fake.
The application stated that Google Docs would like to read, send, delete and manage the recipient’s email and manage their contacts — requests common to several applications that use Google as an authentication mechanism.
Once the permission was granted, the attacker gained access to the victim’s address book, which allowed the attack to go viral swiftly.
The OAuth Vulnerability
The attack leveraged OAuth, “a ubiquitous industry standard protocol [that provides] a secure way for Web applications and services to connect without requiring users to share their account credentials with those applications,” said Ayse Firat, director of analytics and customer insights at Cisco Cloudlock.
“Because it’s so universally adopted by almost all Web-based applications and platforms — including consumer as well as enterprise applications such as Google Apps, Office 365, Salesforce, LinkedIn and many others — it provides a broad attack surface,” she told TechNewsWorld.
OAuth 2.0 is highly sensitive to phishing because every website using it asks end users for the username and password of their master identity. Cisco CLoudlock has identified more than 275,000 OAuth apps connected to core cloud services, such as Office 365, compared with only 5,500 three years ago.
OAuth-based attacks “bypass all standard security layers, including next-generation firewalls, secure Web gateways, single sign-ons, multifactor authentication and more,” Firat cautioned.
The Ramifications of Using OAuth
With software vendors increasingly putting their applications in the cloud, how great a risk do OAuth’s vulnerabilities pose for end users?
“Most cloud services are pretty secure, and OAuth-based attacks likely will not be successful if services depending on the protocol are otherwise secured,” said Michael Jude, a program manager at Stratecast/Frost & Sullivan.
OAuth authentication “is bigger than just online apps,” he suggested. “It’s also a basic establishment protocol that could become important in social media efforts to become more akin to common carriage operations for communications.”
OAuth “has to be done right, or there’s no future for social media-mediated communication services,” Jude warned.
Protecting Against OAuth-Based Attacks
Organizations need to develop a high-level strategy as well as a specific application use policy to decide how they will whitelist or ban applications, and share this vision with their end users, Firat suggested.
Individual users should go into their Google account security settings and revoke permissions to applications they don’t know or trust, she recommended. They also “should never grant permissions to applications that request excessive access.”
Efforts have been launched to incorporate stricter security requirements into OAuth, Frost’s Jude said, “but I haven’t heard of any particular availability.”






















































