Security risks from instant messaging networks and spam-clogged e-mail inboxes are forcing corporations to finds ways to either limit employee access or clamp down with improved security.
Financial firms have an added burden. They must treat instant messages the same as e-mail communication and ensure that workers comply with federal security regulations. Companies that do not have monitoring software in place and rules for employees’ use of instant messaging are flirting with security disaster.
Companies that do not block spam or filter it before reaching workers face increased costs from added time workers spend wading through messages. This contributes to lost productivity and lost business opportunities.
Widespread IM Use
Gideon Stein, the CEO of OmniPod, which markets a secure closed network messaging product designed to eliminate security risks, warns that the two main security issues with instant messaging on consumer networks in the workplace is the spread of worms and the ability to exchange files. Both of these issues present real security risks for unauthorized data access on enterprise networks.
Several vendors now provide specialty products to help corporations plug security holes caused by instant messaging and e-mail spam.
Unmanaged instant messaging is becoming a major problem in the workplace, security experts warn. According to Francis Costello, chief marketing officer for Akonix Systems, a provider of software to manage instant messaging and e-mail, 80 to 90 percent of all companies have some instant messaging in use by employees.
About 80 percent of the IM activity is done by employees using free messaging services like Yahoo, MSN Messenger and AIM (AOL’s service).
If the companies are part of the financial industry, the use of instant messaging is part of the company’s communication services and must meet federal security compliance.
Security Issues at Stake
“The growth of instant messaging in the office is unbelievable,” OmniPod’s Stein said. Costello, of Akonix, agreed, adding that instant messaging is real time communication in the workplace.
“Instant messaging is now a legitimate business communications tool,” Costello said.
When instant messaging is so vital to conducting business, corporations have to lock down the security risk. That necessity is now required by regulations that govern financial companies using the Internet.
“Instant messaging must be treated the same as e-mail to meet federal regulations,” Costello said. Opinion letters from regulatory agencies state that companies must archive IM conversations for seven years and be able to produce them on demand.”
Add to this activity file-sharing from peer-to-peer networks and similar file swapping among workers and the problem worsens.
Costello said that punishment for non-compliance varies by industry.
“Clearly there are severe penalties for financial institutions that don’t comply with IM and e-mail regulations. In some industries, just blocking the messages isn’t an option,” he said.
Scope of IM Problem
OmniPod’s Stein does not see much sense in allowing employees to use public instant messaging programs.
“Public IM has network vulnerabilities and is full of security holes,” Stein told TechNewsWorld.
According to Akonix Systems, more than 100 new corporate security threats targeting IM and P2P systems were identified in the first quarter of 2005. This marks a more than 400 percent increase over the same period last year and more threats than were identified in all of 2004.
“Since the start of 2005, IM networks have been on the receiving end of an unprecedented barrage of security attacks,” Costello said. “Virus writers, hackers and scammers are becoming more sophisticated in their approach to vulnerable, insecure IM clients and networks, distributing not just viruses and malware, but putting together blended attacks and phishing scams.
He said that unmanaged and unauthorized use of IM within enterprise networks presents an increasingly serious threat to corporate security.
Spam Out of Hand
Mark Ramos, president of Granite Software, which offers e-mail filtering products, said the latest trends in e-mail attacks are making business communication very difficult.
Spam is becoming a content-management problem in the workplace.
“The commerce world sells via e-mail. Individuals have to be able to manage e-mail so one method doesn’t fill all security situations,” he told TechNewsWorld.
Attackers Getting Better
According to Akonix officials, the increase in security threats in 2005 are due to three major factors.
One is the continued rapid adoption of instant messaging by enterprise employees for business communications, often without knowledge of management. Virus writers see IM networks as a new vehicle for entry into networks.
A second factor is the increased perimeter security for other attack methods. IT managers are making it more difficult to enter networks by more conventional means.
The third factor is the increased sophistication of attacks. These include published methods that encourage copycats, multiple mutations of initial attacks and migration of new threats, such as social engineering and phishing, to IM systems.
Replace Public Networks
Stein believes that the best security for instant messaging in the workplace is a private messaging network. OmniPod offers a secure on-demand instant messaging application server for enterprise subscribers.
To date the company has more than 300 customers. The system includes an optional file-sharing component.
OmniPod’s system is a closed network that requires authorized clients and their customers to log onto the network. All messages on the system are encrypted, and users can be granted varying levels of access so corporate users are not accessible by customers or office workers.
The system has an interface with public consumer IM networks such as MSN Messenger and AOL’s AIM. OnmiPod filters and encrypts all traffic so security is maintained.
Stein said the server can handle from 50 users up to 40,000. The cost averages $5 per user per month and scales downward based on volume of subscribers.
Manage IM Threats
Akonix’s Costello sees a better result from imposing security on the corporate network to safeguard against IM abuses.
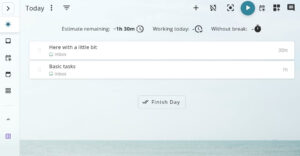
Akonix systems offers instant messaging management software for business. This software secures messages sent over Yahoo Instant Messenger.
Costello said the software maps all instant messaging activity and provides the ability to monitor network perimeters by checking all outgoing traffic.
The software can stop suspicious messages identified by a set of rules and permissions. IT managers can set up policies, monitor activities and filter content to meet security compliance requirements of regulatory agencies.
The cost is based on the number of users. Costello said entry level security for 50 users would cost about $6,000. The cost for 1,000 users within a company would average $25 per user.
Apply Jamming
Granite Software’s Ramos, said his company has developed a product for Lotus Notes that helps to solve the e-mail spam problem. It can link to POP3 e-mail clients also.
Called SpamJam, the software application lets network administrators manage individual filtering settings or allow individual users to configure their own mail filtering.
The Base License for SpamJam covers 10 users on a single server for $995.00
SpamJam has become a big hit in New York State’s Essex County. Stephen Towne, network coordinator for Essex County, has used the product for one year.
“I chose this product because spam on the county’s computers was out of control and other products didn’t solve the problem,” he said.
Towne explained that the biggest selling point for SpamJam is its ability to be configured to meet different levels of filtering.
For instance, a health department member teaches about sex, so she needs mail that contains words related to that topic, so e-mails with those words should not be filtered out as spam.
Another worker in the public health administration office routinely got 50 spam messages a day and took as much as 45 minutes to sort through her e-mail.
“Now she doesn’t spend any time on that task,” Towne said.