
It seems like it was just yesterday that talking on a mobile phone made you cool. You were obviously important, walking around with the confidence that you could be reached at all times. Well, times have certainly changed. Roughly half the planet’s population (over 4.1 billion people) now pay for what was once limited to a select few, according to a recent United Nations survey.
However, the widespread adoption of mobile phones is just one way communications have changed in the last 10 years, fostered in large part by the dramatic growth of the Internet. We want the ability not only to talk anywhere and anytime to anyone, but also to transact (banking, retail, gaming, business, etc) at our convenience — most notably through the Internet.
For example, more than 50 million people in the U.S. had undertaken some sort of online banking by the end of 2008, according to comScore, with many replacing traditional ways of transacting (e.g., checks) with electronic alternatives (e.g., online billpay).
So What?
What does this mean, other than we get to talk when and where we want to, and we don’t have to be in the office or go to a bank to actually get things done?
Well, it means a few things:
- 1) the mass adoption of both the internet and mobile devices has attracted criminals who are aggressively conducting their trade on line;
2) mobile devices can actually be used by organizations today to help increase security; and
3) the convergence of the Internet and mobile devices, combined with the sophistication of those devices, is driving new user behaviors that need to be addressed quickly.
Criminals Get It
Around the same time that it was ber cool to have a mobile phone, hackers were a disorganized bunch intent on creating mayhem, with only a few focused on trying to make money. Again, times have changed.
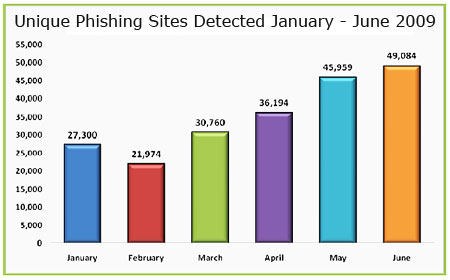
No longer is the threat from the lone basement hacker. Instead, sophisticated criminal organizations are intent on defrauding users. There were 49,084 active phishing sites detected in June 2009 alone, according to the latest report. That’s the second-highest number recorded since APWG began reporting on this measurement.
Desktop and mobile users are being heavily targeted because phishing is one of the most common ways malware and malicious links are delivered to end-users. The results are significant: Analyst firms regularly cite fraud losses for individuals in the billions each year, and businesses are being targeted by criminals because of their large bank accounts. Interestingly, while end-users are often covered by a bank for losses, business accounts are not!
Although not as prevalent as desktop attacks, mobile devices are also being targeted. There are regular announcements in the media around particular operating system flaws, as well as attacks. For example, ‘SMiShing’ attacks (phishing using SMS text messages) are increasing. Users are lured to click on a link that triggers a variety of consequences, ranging from going to a simple spam site to full compromise of their device.
The bottom line: Criminals are organized and focused on getting your money. The more places your electronic footprint wanders, the more opportunity there is for a fraudster to focus his sights on you.
Unique Opportunity
The widespread use and sophistication of mobile devices provides organizations with a unique opportunity to increase transaction security with minimal cost, and without unnecessarily inconveniencing end-users. Today, there’s a diverse array of authentication capabilities for online site access. However, a mobile device can be a very effective, convenient and secure alternative means of authentication.
There are many ways a mobile device can be used for strengthening authentication, such as storing a secret image of a random personal grid that can be used for authentication during a session, installing an application that emulates a hardware OTP token, or sending an out-of-band message (via voice, SMS, or email) each time increased security is required.
Out-of-band is one of the more secure methods. Users can be presented not only with random passcodes, but also with transaction details to verify that they are actually doing what they wanted to.
In all of these approaches, users can simply carry their mobile device with them, as opposed to carrying a secondary device.
Primary Access Points
While mobile phones present an opportunity to increase online security, there are challenges. The newest mobile handsets, like those powered by Google’s Android OS and Apple’s popular iPhone — as well as RIM’s BlackBerry units and a slew of smartphones running on Symbian, and Windows Mobile — all make it possible to actually use your phone to undertake transactions online.
Although such mobile use is relatively small today, it is likely to increase rapidly –growing from 10 million active users in 2009 to more than 53 million active users in 2013, according to TowerGroup. However, the challenge presented by this opportunity is that the devices themselves are not necessarily secure.
Ninety-three percent of users do not secure their devices, while more than 60 percent of smartphones typically contain sensitive information such as login details, according to a recent UK government survey conducted by Trend Micro. While more-advanced fraud detection solutions can differentiate between a mobile and computer user, this may not help if someone steals the actual device!
In the enterprise world, more and more organizations are deploying smart devices for increasing connectivity to the business. For example, Apple’s Q3 2009 earnings call highlighted that approximately 50 percent of Fortune 500 companies are piloting or deploying the iPhone. This is, of course, in addition to the strong presence that RIM already has in the business world.
While these solutions do provide some level of security and policy control, 89 percent of security professionals have doubts about mobile phone security, while 46 percent of surveyed organizations do not have a specific security policy for mobile phones, according to the 2009 Mobile Security Survey by Goode Intelligence and Acumin Consulting.
Whether it is for consumer or enterprise use, security for devices currently lies primarily in the hands of the manufacturers and OS vendors. However, the industry has not yet come to grips with how to truly secure the device itself in the face of existing and emerging threats.
Ripe for Innovation
The explosion of both the Internet and mobile device usage has landed us in an interesting place in history. Mobile devices are increasingly sophisticated and can be used today to increase security for traditional online transactions.
On-device security is still lagging in focus, with most mobile device vendors more interested in usability and functionality. The industry is ripe for innovation in the security space, building on the inherent strength of mobile devices today to provide end-users not only with the ability to order a pizza online at midnight, but also the confidence to do so securely.
Steve Neville is director of identity at Entrust, a provider of solutions to protect digital identities and information for enterprises and governments.











































