A flaw in electronic hotel door locks from Assa Abloy could allow hackers to access guest rooms and other secure locations at millions of properties around the world, F-Secure researchers have discovered.
Software updates were issued to fix the flaw in the smart locks, called “the Vision by VingCard,” after F-Secure notified and worked with Assa Abloy over the past year.
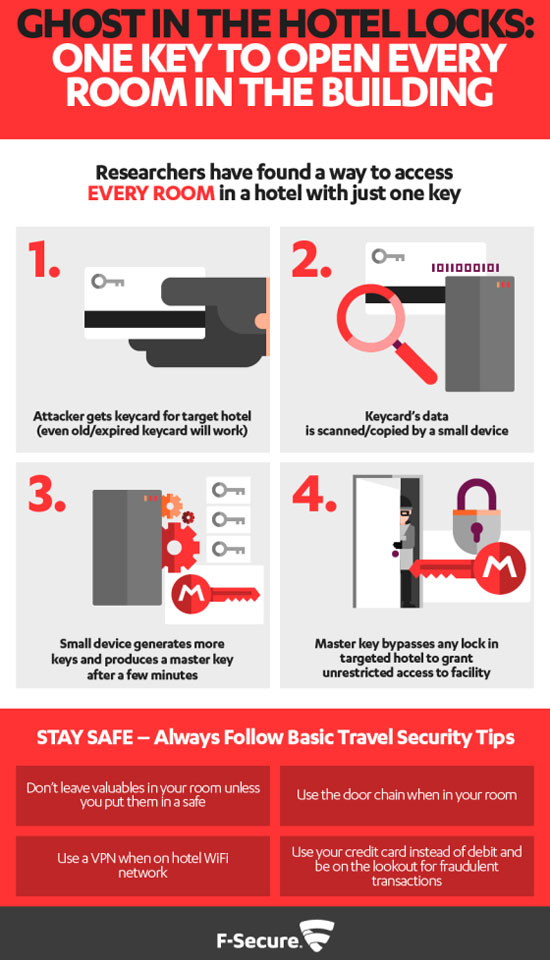
The researchers had found a way to make a master key using information from a key card for any room — including closets and garages, and even long-expired or discarded keys. The method would have allowed hackers to carry out an attack without being noticed.
Persistence Pays Off
The researchers started looking into the issue after a 2003 incident in which a colleague’s laptop was stolen during a security conference. The hotel staff reportedly had not taken the reported theft seriously, saying there were no signs of forced entry or unauthorized room access.
Over the years, the researchers spent thousands of hours, on and off, investigating the incident. They eventually homed in on a lock known for having strong security and high quality.
“Only after we thoroughly understood how the system was designed were we able to identify seemingly innocuous shortcomings,” said Timo Hirvonen, senior security consultant for F-Secure. “We creatively combined these shortcomings to come up with a method of creating master keys.”
No actual hotel rooms were compromised during the research, according to the firm.
The vulnerability applies only to the Vision by VingCard product, Hirvonen told the E-Commerce Times, adding that F-Secure agreed with Assa Abloy to withhold the mechanism of the vulnerability.
Multiple factors impact the effectiveness of electronic door locks, he pointed out, noting that encryption is used to protect the confidentiality of the data on the key card.
“Encryption raises the bar to start analyzing the system,” Hirvonen said. “However, encryption is not a silver bullet — the encryption key has to be securely generated and stored.”
Hotel Review
Marriott International confirmed that Assa Abloy notified the hotel chain about the vulnerability in a version of the company’s locking system.
“We are currently working with the vendor to understand the impact to our hotels,” said spokesperson Hunter Hardinge.
The company had been issued a software patch by Assa Abloy and was working to deploy the patch as fast as possible, she added.
The hack is based on cryptographic weaknesses of older-generation door locks, said Andrew Howard, chief technology officer at Kudelski Security, based on reports he has read.
The vulnerability allows the hackers tools to cycle through potential door access codes until the right one is found, he told the E-Commerce Times.
This report is a reminder of the vulnerability of remote locks, particularly at a time when companies increasingly are selling smart lock devices controlled through mobile apps, said Brian Martin, vice president of vulnerability intelligence at Risk Based Security.
“All of this is a serious warning that these systems need to have strenuous testing before they are pushed to market,” he told the E-Commerce Times.
Just last year, New York Attorney General Eric Schneiderman reached a settlement with Safetech Products over allegations that its Bluetooth padlocks and wireless door locks were not secure.
Researchers had found that the company transmitted password information from the locks to mobile phones without the encryption necessary to hide the data from hackers. The default passwords on the locks were figured out easily using brute force attacks.
In 2016, researchers at the University of Michigan, working with Microsoft, found a vulnerability in Samsung SmartThings IoT systems. It allowed them to access PINs on electronic door locks and to exploit a SmartApp in order to create a spare door key. The team notified Samsung and worked with the company to address the flaws.














































