
Uploaders to eDonkey.com, Bit Torrent and other file-sharing networks beware: The commercial equivalent to Big Brother is watching you.
BayTSP, a leading provider of online intellectual property monitoring and compliance systems, last month began offering a service aimed at software, movie and music pirates. FirstSource is an automated system that identifies the first users to upload copyright- or trademark-protected content to major peer-to-peer (P2P) networks.
The service gives owners of intellectual property a way to identify the first individuals who upload illegal content. It also allows companies to track all subsequent users who download and share a particular file.
Evidence for Court
With this information in hand, intellectual property owners can produce evidence in court to substantiate piracy charges.
“Pirated copies of movies and software typically appear online within hours of release,” Mark Ishikawa, CEO of BayTSP, said. “Identifying and taking action against the first uploaders can greatly slow the distribution of illegally obtained intellectual property and might make users think twice before doing it.”
The FirstSource concept was tested successfully in BayTSP’s computer labs. “We’ve been working with this system in-house since the summer,” Ishikawa told TechNewsWorld.
He said the system is based on a unique search protocol, but declined to provide specifics. He added that the process is similar to conducting an Internet search with Google.
Ishikawa said the concept has proved successful in trials conducted since the last quarter of 2004.
“We don’t have to touch the file first. We identify the first person to make it available,” Ishikawa said.
Initial tests of the FirstSource service indicate that several thousand copies of a movie available for download on the eDonkey.com and Bit Torrent networks can be traced back to the initial uploaded file.
Ishikawa said the FirstSource service is already in use for some of BayTSP’s clients for gathering evidence to be used in pending litigation.
How It Works
“Just watch for the news when the first major case breaks,” he told TechNewsWorld.
EDonkey and Bit Torrent are two of the most popular file sharing networks and use a technique called swarming that allows users to download slices of a file, according to BayTSP. These slices could come from a pirated movie or software application.
The swarming technique lets multiple users access the files for download simultaneously. As users download a file, they also share the portions they’ve already received.
FirstSource monitors for the first uploads of a client’s intellectual property to the eDonkey and Bit Torrent networks. When the system spots a file name matching the client’s content, it initiates a download to confirm that the file is what it appears to be.
Once the content is validated, the FirstSource system captures the Internet Protocol address and identifying information of other users downloading and sharing the pirated material.
The system also logs which portions of the file that each user shares. This data is stored in an infringement database as evidence in the event the client decides to pursue litigation against the file sharers.
Offenders Put on Notice
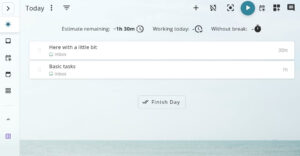
The FirstSource system permits BayTSP’s clients to monitor the tracking via a Web-based interface. When computer users are identified as being a tracked downloader or supplying copyrighted material, they receive a notice of violation.
Clients have the option of automatically or manually issuing these take-down notices under the Digital Millennium Copyright Act. The process is so efficient that sometimes the notices can be served while the downloads are still in progress.
The take-down notice is directed at both the ISP operators and the individual file-sharers.
U.S.-based ISP operators are directed to comply with the Digital Millennium Copyright Act by blocking access to infringing files. The notice directs the ISP owner to reply to the infringement notice and verify that the infringing material is blocked. According to the notice, International ISPs are bound by the Bilateral Treaty and/or the Berne Convention to similarly block access to the copyrighted material.
The notice sent to identified users announces that copyrighted material belonging to a client of BayTSP is publicly available on the users’ computers without the proper authorization and/or license.
Effective Deterrent
The notice states: “Under the DMCA (USA) and the Bilateral Treaty and Berne Convention (International), this constitutes a copyright violation. You must promptly remove the infringing works. We also strongly recommend you reply to the infringement notice verifying removal of the infringing files. Please note that blocking access/removal of infringing material does not relinquish our client’s right for further action against you.”
Ishikawa said the FirstSource scans find between 3.5 million and 5 million copyright violations per day.
BayTSP officials are counting on word of their success rate spreading quickly to file-sharers who exchange illegal files. The penalties, noted Ishikawa, are too severe not to take notice. He hopes to discourage people from taking the risk.
“I could be the best Internet op around. I still could never stop the piracy completely,” Ishikawa said.
“Theft of intellectual property is so prevalent on the Internet that I will never put myself out of business,” he said.




















































Just to be clear… How does it monitor the first upload of a bittorrent file to a network, when bittorrent doesn’t use a network? All it uses is a tracker to verify who is using the same torrent control file. The file itself does not contain anything other then names and some reference to the primary source. I could decide to make the name of my own application ‘Tina Turner – Golden Eye.exe’ and due to the complications involved with various bitrates using from MP3, nevermind the numerous other music format, file types, bitrates, compression methods, etc., there is no way they can tell the difference between that being a song or an application. It only gets worse if I call it something like License To Kill (also a name from The Best of Bond CD). How do they know just from the file name that the torrent points at music, not a zip file of a game I made or anything else. BayTSP’s system might work for ‘other’ centralized systems, but for bittorrent or even eDonkey, it is absolute bullshit.
Yea i doubt these people even know what bittorrent is…i saw the edonkey website and it seems to be something along the lines of limewire, just a little more advanced. These idiots dont know that bittorrent uses a completely different system. edonkey: 1 user uploads and people download the whole file, then they can upload….vs bittorrent: the first person uploading and the next 1 to infinite number of people uploading can be seconds to milliseconds from each other. Whoever wrote this article should be castrated and fired.
Well they are doing something effective because my ISP suspended my account along these lines and identifed edonkey as the source. They knew the file name, type of file and had all logs of the ports being used. It’s real…..