Researchers atMIT and theUniversity of Innsbruck last week announced that they had designed and constructed the world’s first scalable quantum computer, a development that could make existing encryption technology obsolete.
They built the computer using five atoms in an ion trap, according to a report published in the journal Science.
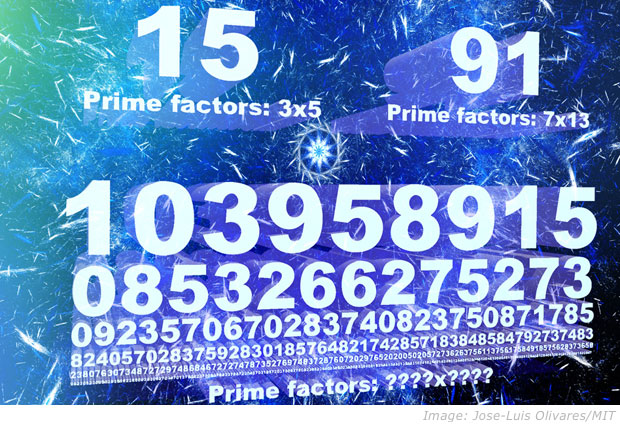
The researchers used laser pulses to carry out an algorithm — conceived in 1994 by MIT Professor Peter Shor — on each atom to correctly factor the number 15. The computer system is designed so that atoms and lasers can be added to factor much larger numbers, creating the world’s first system that can scale Shor’s algorithm.
The algorithm is the most complex quantum algorithm known, but it can be upgraded in a laboratory setting, said Isaac Chuang, professor of physics, electrical engineering and computer science at MIT.
Chuang, considered a pioneer in the field, designed a computer in 2001 based on a single molecule that could be held in superposition and manipulated through nuclear magnetic resonance to factor the number 15. Those results, published in the journal Nature, were not scalable and were considered experimental.
The New Math
Unlike traditional computing, which relies on 0s and 1s to carry out algorithmic instructions, quantum computing relies on qubits, which are atomic-scale units that can be 0 and 1 simultaneously, a state known as “superposition.” That allows a supercomputer to carry out two separate lines of instructions at the same time, for example.
“We’ve been hearing about quantum computers for many years and the concerns about how they may be able to break existing encryption schemes,” said Steve Pate, chief architect atHyTrust.
A lot of the work came from the academic community and resulted in the DES algorithm being replaced with 3DES and later AES, which is widely used now, he told TechNewsWorld.
“3DES — pronounced trip-DES — is a mode of the DES encryption algorithm that encrypts data three times. Three 64-bit keys are used, instead of one, for an overall key length of 192 bits. The first encryption is encrypted with a second key, and the resulting cipher text is again encrypted with a third key,” Pate explained.
“This improves the security of the algorithm and uses a larger key size but makes the overall encryption/decryption time longer,” he said.
Out of the Laboratory?
The MIT development shows that quantum computing has moved beyond an idea and into a question of implementation, said Kevin O’Brien, CEO ofGreatHorn.
“The implications here are twofold,” he told TechNewsWorld. “First, this development suggests that quantum computing is becoming a question of scale rather than theory, much as the development of smaller chip sizes allow for increased complexity in traditional computing.”
The second point is that “the question of relying on the exchange of keys, even with larger key sizes, will not be sufficient in a quantum-enabled world,” he said. New types of encryption will be required.
Implementing quantum computing on a large scale is not cost effective, said Mike Jude, program manager at Stratecast/Frost & Sullivan.
“The technology to maintain a 5-qubit computer is very complex and difficult,” he told TechNewsWorld, noting that it involves supercooling and laser entrapment. “These are not likely to become desktop components any time soon. In fact, the very act of using a qubit destroys it, so a 5-qubit computer is good for one solution before it has to be rebuilt.”
“While we still have a few years before quantum computers become mainstream,” Eli Dourado, director of theTechnology Policy Program at the Mercatus Center at George Mason University, told TechNewsWorld, “governments and a few other security-conscious organizations should start using quantum-safe encryption techniques now.”