Future Tense Central and Etransfr have debuted Chadder, an app that sends private encrypted messages.
The app is one of a growing number of security products built around encryption technology and touted as secure that hit the market following Edward Snowden’s massive data dump revealing the extent of the U.S. government’s reach into consumers’ digital lives.
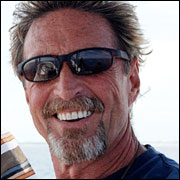
Chadder stands out, though, because it was developed under the direction of security pioneer John McAfee, who in recent years has become embroiled in a real-world murder mystery. Whether McAfee’s signature on this product will give it legs or squash it as it comes out of the gate remains to be seen.
How It Works
Chadder is based on key server encryption, which means even Chadder can’t see a sender’s message, McAfee said. Only the recipient, who has the key, can read it.
Chadder currently is available at Google Play and the Windows Phone Store. An iOS version is being tested and will available on iTunes in coming weeks.
Many Security Claims
Chadder’s creds are not impressive, suggested Ken Westin, a security researcher for Tripwire.
“Whenever a new app comes out claiming to be secure and private, it should be met with skepticism,” he told TechNewsWorld. “Many developers have made these claims, and they have turned out to be less than accurate.”
Chadder’s encryption engine — but not the app itself — was vetted by an independent third party security firm, Future Tense Central spokesperson Andrew Defee told TechNewsWorld.
That should only be the start of due diligence for a security technology, according to Westin.
“If Heartbleed and other recent security events have taught us anything, it’s that when a vendor says they’re using encryption it should be the start of a more detailed conversation — not the end of it,” he said.
Numerous reviews of the app have pointed to several bugs in the registration process, Westin pointed out, which doesn’t inspire confidence. “It leaves me wondering what other bugs security researchers will find now that the application has launched.”
Furthermore the app’s association with McAfee is hardly a plus and could well be a detriment, he said, as it could make the application and its infrastructure a more appealing target for cyberattackers.
The ‘McAfee’ Name
Of course, the current generation of cyberattackers might not recognize the “McAfee” name.
John McAfee effectively has been out of the technology market for two decades, “and this is a market that cycles as often as twice a year in some segments,” noted Rob Enderle of the Enderle Group. Five years is a lifetime.
“It is impossible for anyone to exit this industry decades ago and then step in and be relevant,” he told TechNewsWorld.
McAfee’s position as a newsmaker in recent years doesn’t help. He made global headlines in 2012, when he became a “person of interest” wanted for questioning in the murder of a neighbor in Belize.
McAfee went to considerable lengths to evade Belizean authorities, fleeing to Guatemala, where he was arrested for entering the country illegally and then deported to the U.S.
Having once been an international fugitive would seem to be in massive conflict with the level of trust that needs to exist with a security product, Enderle said.
More to the point, Enderle is dismissive of Chadder’s security claims.
“Simple key encryption like the technology Chadder appears to be providing is easily penetrated by security services, and any messaging app, to be successful, has to be as easy to use as what it replaces,” he explained.
Also, the security gaps that usually compromise systems would not be addressed by a messaging app, no matter how secure, Enderle said, “because they provide remote control of the client device to the hacker who could then look at any message repository the user had access to — including Chadder.”




















































